RACGP accreditation IT requirements explained. Data backup, access controls, encryption, audit trails and the IT checklist your Perth practice needs before the assessor arrives.

# RACGP IT Requirements: What Your Practice Needs for Accreditation in 2026
If your general practice is preparing for RACGP accreditation — or reaccreditation — there is a good chance IT is not the first thing on your mind. Most practice managers focus on clinical governance, infection control, and patient safety documentation. These are critical areas, and rightly so.
But IT is woven through the RACGP Standards for General Practices (5th Edition) in ways that catch many practices off guard. Data backup failures, missing access controls, and undocumented security procedures are among the most common findings that create problems during assessment.
This guide walks through the specific IT requirements your practice needs to address, the common gaps we see across Perth clinics, and how to prepare before the assessor arrives.
What the RACGP Standards Say About IT
The RACGP Standards (5th Edition) do not have a single "IT chapter." Instead, information technology requirements are embedded across multiple standards and criteria, particularly within:
- Standard 1: Communication and patient participation — electronic communication, patient portal access, secure messaging
- Standard 2: Rights and needs of patients — privacy of health information, consent for electronic records
- Standard 4: Comprehensiveness of care — clinical information systems, decision support, prescribing software
- Standard 5: Practice management — data security, backup and recovery, business continuity, workforce training
More information: RACGP Computer and Information Security Standards
The IT Checklist for Accreditation Readiness
Based on the RACGP Standards and CISS framework, here are the IT requirements your practice should have documented and operational before accreditation.
Data Backup and Recovery
- Automated daily backups of all clinical data (Best Practice, Medical Director, Genie, or your platform of choice)
- Offsite backup copy stored separately from your practice servers — ideally in an Australian data centre
- Regular backup restore testing — at least quarterly, with documented evidence that restores were successful
- Documented backup and disaster recovery plan covering scenarios including server failure, ransomware, fire, and theft
Access Controls and User Management
- Individual user accounts for every staff member — no shared logins
- Role-based access levels — reception staff should not have the same system access as GPs
- Strong passwords enforced (minimum 12 characters recommended)
- Multi-factor authentication (MFA) enabled on email, remote access, and clinical systems where supported
- A documented process for disabling accounts when staff leave the practice
- Audit logging enabled on clinical software to track who accessed what and when
Network and Physical Security
- Business-grade firewall with current firmware — not a consumer router
- Servers and network equipment physically secured in a locked area
- Encrypted Wi-Fi with separate networks for clinical devices and patient/guest access
- Workstation screen lock policies (auto-lock after 5 minutes of inactivity)
- Endpoint protection on all workstations — not just antivirus, but modern endpoint detection and response
Software and Patch Management
- Clinical software kept on current supported versions (check with your vendor)
- Operating system patches applied regularly — ideally within 14 days of release for critical updates
- Third-party application patching (Adobe, Java, browsers) — automated where possible
- A documented schedule for when patches are applied (typically outside clinical hours)
Encryption
- Encryption at rest on servers and workstations (BitLocker on Windows, FileVault on Mac)
- Encryption in transit for any remote access or cloud services (TLS/SSL)
- Encrypted email for sending patient information externally
- Encrypted backup storage
Incident Response
- A documented incident response plan covering data breaches, ransomware, and system failures
- Knowledge of Notifiable Data Breaches (NDB) scheme obligations — when and how to report to the OAIC
- Contact details for your IT provider's emergency support line
- Staff awareness of what constitutes a reportable breach
Staff Training
- Annual cybersecurity awareness training for all staff
- Training records documented (assessors may ask for evidence)
- Phishing awareness — staff should know how to identify and report suspicious emails
- Documented acceptable use policy for practice IT systems
Common IT Gaps That Fail Accreditation
Across Perth practices we support, these are the IT issues that most frequently cause problems during accreditation assessments:
1. Backups Exist but Have Never Been Tested
This is the single most common gap. The backup runs every night, the logs show green, and everyone assumes the data is safe. But when was the last time someone actually restored from that backup to verify the data is complete and usable? If the answer is "never" or "I'm not sure," that is a problem the assessor will identify.
2. Shared Login Accounts
We still see practices where multiple staff share a single Windows login or clinical software account. This makes it impossible to maintain an audit trail of who accessed patient records — a fundamental requirement under both RACGP Standards and the Privacy Act.
3. No Documented IT Security Policies
Having good security practices is not enough — you need to have them documented. Assessors look for written policies covering acceptable use, password requirements, data handling, and incident response. Many well-run practices have strong IT but no documentation to demonstrate it.
4. Outdated Software and Unpatched Systems
Running a version of Best Practice or Medical Director that is no longer supported, or Windows workstations that have not been patched in months, creates both a security risk and an accreditation risk.
5. No Separation of Clinical and Guest Networks
If your patient Wi-Fi runs on the same network as your clinical workstations and servers, that is a security vulnerability. Network segmentation is a basic requirement that is increasingly scrutinised.
How to Prepare Your IT Before the Assessor Arrives
Accreditation preparation should start at least three months before your assessment window. For IT specifically:
3 months out:
- Conduct an IT security audit against RACGP CISS requirements
- Identify and document all gaps
- Begin remediation of critical issues (backup testing, access controls, patching)
- Complete all technical remediation
- Draft or update IT security policies and procedures
- Conduct staff cybersecurity awareness training
- Perform and document a backup restore test
- Final review of all IT documentation
- Verify all systems are patched and current
- Confirm backup monitoring is active and restore tests are documented
- Brief practice manager on IT-related questions the assessor may ask
- Have IT documentation readily accessible (printed or digital)
- Ensure your IT provider is available by phone if the assessor has technical questions
- Be prepared to demonstrate backup logs, access control settings, and patch status
Getting Expert Help
If your practice does not have an IT provider with healthcare accreditation experience, the preparation process is significantly harder. Generic IT companies often do not understand RACGP Standards or CISS requirements, which means they cannot tell you whether your IT environment meets the benchmark.
SkyComm has supported Perth GP practices through accreditation and reaccreditation cycles for over 15 years. Our managed IT services include proactive compliance monitoring, documented security policies, regular backup testing, and the technical evidence your assessor will look for.
We also provide standalone accreditation IT assessments for practices that want an independent review of their IT readiness before the formal assessment.
Frequently Asked Questions
Is RACGP CISS mandatory for accreditation?
CISS itself is guidance, not a mandatory standard. However, accreditation assessors use CISS as the benchmark for evaluating IT security. Practices that align with CISS are far less likely to receive findings related to IT.
What clinical software do I need for accreditation?
You need clinical software that is conformant with ADHA requirements and capable of supporting electronic prescribing, Medicare Online claiming, secure messaging, and My Health Record integration. Best Practice, Medical Director, and Genie Solutions all meet these requirements.
How often should backups be tested?
At minimum quarterly, with documented evidence. Monthly is better practice. Skycomm tests client backups monthly and provides documented reports.
Do I need a dedicated IT security policy?
Yes. Assessors expect to see documented policies covering data security, acceptable use, access management, and incident response. These do not need to be lengthy — clear, practical documents are better than verbose policies nobody reads.
Next Steps
If your practice has accreditation coming up and you are not confident in your IT readiness:
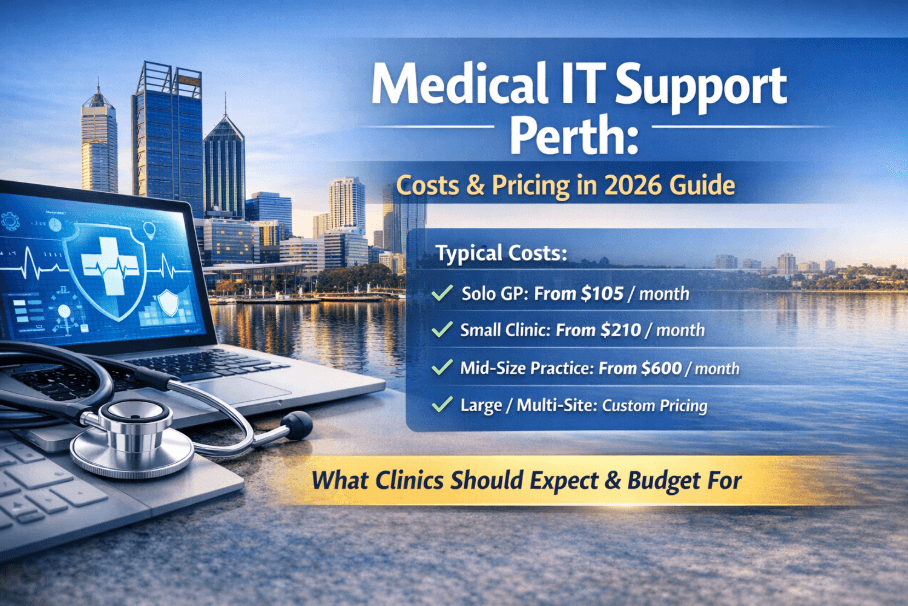
- Call: 1800 957 977
- Book a Free IT Assessment: Contact Skycomm
Related Reading
- Best Practice vs Medical Director: Which Is Right for Your Practice?
- Medical IT Support Perth: The Complete Guide (2026)
- Healthcare Cybersecurity in Action: Clinic IT Review
- How to Compare Medical IT Providers in Perth
- IT Setup Checklist for a New Medical Clinic
- Cybersecurity Services
- Managed IT Services
- Backup and Disaster Recovery
SkyComm IT Solutions
Perth's leading medical and business IT support provider. Trusted by healthcare practices, law firms, and businesses across Western Australia for over 20 years.